Police are using facial recognition software, this isn’t new, but it is going to be a growing tactic in coming years.
Leicestershire Police is one of the UK forces that is pushing the boundaries with using the technology for policing purposes, but it has been heavily criticsed for its apparent underhand tactics. As with all collection of a personal data (an image is undoubtedly personal data) the police have to consider data protection.
Below is a copy of the Privacy Impact Assessment (PIA) the midlands force conducted before using its NeoFace technology. The bulk of document sees the police go through the Data Protection Act’s principles and considers how the use of the technology complies, or doesn’t comply, with it.
The PIA, obtained under FOI, has been sat in my inbox for a couple of weeks and as I am trying to post more of the bits I obtain under the Act onto here I’ve decided to throw it up. I’ve only had rapid scan of the document but here a few bits I found interesting:
- The technology can select up to 200 images – it says they’re not based on gender, race, or age – from two databases of images fed into its system. The biggest database being CIM, which has 104,000 images.
- The police has decided not to include metadata at prseent
- It can used images captured from body cams (although I doubt the quality is high enough for images to be matched) and social media, as well as CCTV.
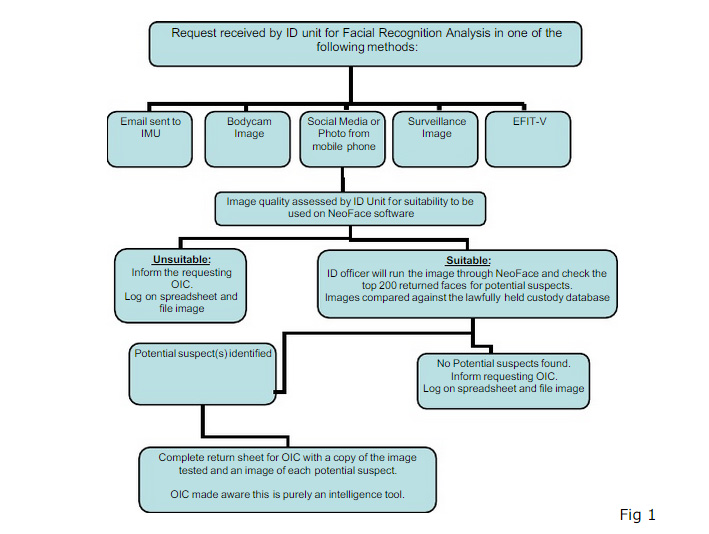
- This is process for running an image through the system:
- The key privacy issues relate around image retention.
- The set-up for the facial recog system is in a secure building, on one computer, separated from the rest of the building.
- The images returned can’t be used as evidence.
- If the technology becomes ‘business as usual’ a new PIA will need to be completed.
- It isn’t a storage system but can be used as a search engine when images need to be removed from the custody system.
- ‘Police partners’ can request to use the system.
- They are considering fitting a security screen around the computer with the tech on.
- Police need to ‘consider the justification for the use of technology to identify individuals involved in other crimes/incidents’.